Last week, when I was working on how to setup the Kerberos SSO for D2 3.1 SP1, I faced some issues due to a documentation that doesn’t seem to be up to date… In fact, our version is D2 3.1 SP1 and there is no specific documentation for SP1. In consequence, I read the D2 3.1 Installation Guide and the D2 4.0 Installation Guide. The first time I read the D2 3.1 documentation, I found it very light and I knew I would have some problems. Fortunately, I already had experience with Kerberos, essentially with the MIT distribution on Linux (how to setup a KDC, kerberize an application, manage users, etc.).
The first thing that is important to know is that as D2 isn’t a WDK client, the setup of the SSO using Kerberos just involves the D2 host server and the Active Directory server. There is no need to setup the Content Store to use Kerberos. So here is the configuration that were used:
- Microsoft Active Directory on Windows Server 2008 R2. Let’s name this server ad001 and the related domain domain.com
- D2 3.1 SP1 on Microsoft Server 2008 R2. Let’s name this server wd231
The second thing that is important to know is that not all Directory Servers are supported. Indeed, Documentum doesn’t support Linux Key Distribution Center (KDC).
1. D2 3.1 documentation steps
The first part of this blog will describe which steps the official D2 3.1 Installation Guide provides to help Administrator to setup a SSO using Kerberos in D2. You will see that those steps aren’t very descriptive but with a little bit of imagination, you could do something with that.
a. Edit the shiro.ini file
Open the file shiro.ini and add the following lines:
[main] D2-Kerberos=eu.c6.d2.web.filters.authc.D2KerberosHttpAuthenticationFilter D2-Kerberos.servicePrincipal=HTTP/computerName.domainName D2-Kerberos.krbConfLocation=C:/Windows/krb5.ini D2-Kerberos.keyTabLocation=C:/computerName.keytab D2-Kerberos.docbases=docbase1,login1,password1,domain1|docbase2,... D2-Kerberos.debug=true [urls] /** = D2-Kerberos
b. On the AD
Create a user on the AD with the computer name of your application server and add the following options:
- Use Kerberos DES encryption types for this account
- This account supports Kerberos AES 128 bit encryption
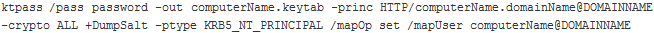
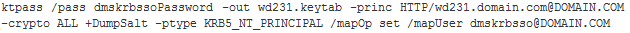
Generate a keytab using the command below. Well in fact the official documentation only display the command and don’t explain what is it or where to execute it.
Transfer this keytab on the D2 host server.
c. krb5.ini
[libdefaults]
default_realm = DOMAINNAME
[realms]
DOMAINNAME = {
kdc = adserver.domainName
}
d. On Windows 7
- Run gpedit.msc
- Expand “Local Computer Policy” / “Computer Configuration” / “Windows Settings” / “Security Settings” / “Local Policies” / “Security Options” / “Network security:
- Configure encryption types allowed for Kerberos”
- Double click “Network security: Configure encryption types allowed for Kerberos”
- Select all.
- Press “OK”
2. D2 3.1 SP1 steps
The second part of this blog will present which steps must be done to get Kerberos SSO working with D2 3.1 SP1. If you only follow steps describes in the official documentation, as some explanations are missing, you will probably get issues. Now here are the steps that were required to get the SSO working on our D2 3.1 SP1:
Let’s begin with the beginning contrary to the official documentation which begin with the end. So logic!
a. On the Active Directory
Create a user on the Active Directory with the following properties:
- Username doesn’t matter (don’t need to be the D2 server hostname). Let’s name this user: dmskrbsso
- Password: dmskrbssoPassword
- Password never expire
- This account support Kerberos AES 128 bits encryption
- Trust for Delegation to any service (Kerberos Only)
- This account support Kerberos DES encryption
This last configuration isn’t mandatory as Kerberos will always use the most secure encryption available (AES 256 in general). So there is no problem if your Active Directory admin doesn’t want to enable DES encryption as this isn’t enough secure.
When the user is successfully created, open an administrator command prompt and create the keytab for D2 using the following command:
This command will create a file named wd231.keytab which should be transfer on the D2 host server. Let’s place this file at the following location: C:/Kerberos/wd231.keytab
b. On Documentum Administrator
Create a repository user with the same Name, Login Name and password as the one created on the AD:
- State: Active
- Name: dmskrbsso
- Login Name: dmskrbsso
- Login Domain: domain.com
- User Source: Inline Password
- Password: dmskrbssoPassword
- Privileges: None
- Extended Privileges: None
- Client Capability: Consumer
This first user will just reflect the new user created on the AD but I think this user isn’t mandatory.
Create another repository user which will be used by the shiro.ini file to connect all other users through SSO:
- State: Active
- Name: d2krbsso
- Login Name: d2krbsso
- Login Domain: domain.com (This is mandatory! The SSO will not work without the AD domain here)
- User Source: Inline Password
- Password: d2krbssoPassword
- Privileges: Superuser
- Extended Privileges: None
- Client Capability: Consumer
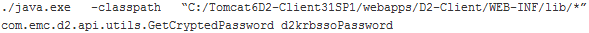
From a command prompt on the D2 server, execute the following command to get the encrypted password of the user d2krbsso:
This command assume that your D2-Client web application is at “C:/Tomcat6D2-Client31SP1/webapps/D2-Client/”. Remember the result of this command as the encrypted password will be needed later in the shiro.ini file. Let’s name this encrypted password userEncryptedPw
c. krb5.ini
Create the file C:/Kerberos/krb5.ini with the following content:
[libdefaults]
default_realm = DOMAIN.COM
[realms]
DOMAIN.COM = {
kdc = ad001.domain.com
}
[domain_realm]
.domain.com = DOMAIN.COM
domain.com = DOMAIN.COM
[logging]
default = FILE:C:/Kerberos/logs/kdc_default.log
kdc = FILE:C:/Kerberos/logs/kdc.log
Don’t forget to create the folder C:/Kerberos/logs/.
d. Edit the shiro.ini file
The shiro.ini file is the file used by D2 to authenticate user through Kerberos. This file could be found at “C:/Tomcat6D2-Client31SP1/webapps/D2-Client/WEB-INF/classes/shiro.ini”. Replace the properties in this file with the following:
[main] D2-Kerberos=com.emc.d2.web.filters.authc.D2KerberosHttpAuthenticationFilter D2-Kerberos.servicePrincipal=HTTP/ D2-Kerberos.krbConfLocation=C:/Kerberos/krb5.ini D2-Kerberos.keyTabLocation=C:/Kerberos/wd231.keytab D2-Kerberos.docbases=docbase1,d2krbsso,userEncryptedPw,DOMAIN.COM D2-Kerberos.debug=true [urls] /**=D2-Kerberos
docbase1 correspond to a repository using Kerberos. You could set more than 1 docbase using the following property:
D2-Kerberos.docbases=docbase1,login1,password1,domain1|docbase2,…
Maybe you didn’t see the difference with the original documentation but if you look at the property named “D2-Kerberos”, you will see that the Java Class D2KerberosHttpAuthenticationFilter isn’t in the same package. In our D2 3.1 SP1, this Java Class is located in com.emc.d2.web.filters whereas the D2 3.1 official documentation indicate it on eu.c6.d2.web.filters. Something funny is that on the D2 4.0 official documentation, this property indicate again another location: eu.c6.d2.portal.server.filters.
e. Verify the Java Runtime Environment
It seems that Kerberos SSO for D2 require a java 1.6 jre. The simplest way to verify this is to check the service configuration of your application server. Another way could be to take a look at the registry:
- Run regedit
- Navigate HKEY_LOCAL_MACHINE / SOFTWARE / Wow6432Node / Apache Software Foundation / Procrun 2.0 / tomcat6D231SP1 / Parameters / Java
- Verify that the JVM parameter point to Java 1.6: C:/Program Files/Java/jre6/bin/server/jvm.dll
This assume that the JAVA_HOME of your application server is C:/Program Files/Java/jre6/
f. Install the Java Cryptography Extension (JCE)
Download Java Cryptography Extension (JCE) for the java version used by the JVM and copy both jars into:
C:/Program Files/Java/jre6/lib/security/
g. Restart
Restart your D2 application server and look for errors on the tomcat error log files:
C:/Tomcat6D2-Client31SP1/logs/tomcat6d231sp1-stdout.YYYY-MM-DD.log
h. User configuration
For D2 Kerberos SSO, there is no need to change anything on user properties. That means that, for example, a Login Domain of LDAP and User Source of LDAP is fine.
i. On client computer
- Run gpedit.msc
- Expand “Local Computer Policy” / “Computer Configuration” / “Windows Settings” / “Security Settings” / “Local Policies” / “Security Options” / “Network security:
- Configure encryption types allowed for Kerberos”
- Double click “Network security: Configure encryption types allowed for Kerberos”
- Select all.
- Press “OK
Please be aware that the D2-Client URL must be detected by Internet Explorer as an “Intranet Site”. This could be done through Internet Explorer options.
This finally concludes the configuration of Kerberos SSO in D2 3.1 SP1. To get a Kerberos ticket, just log in on the client machine with a user defined in AD and if you have followed the steps above, SSO should work. If this is not the case, please let me know and I might be able to help.
Good luck!
![Thumbnail [60x60]](https://www.dbi-services.com/blog/wp-content/uploads/2022/08/MOP_web-min-scaled.jpg)
![Thumbnail [90x90]](https://www.dbi-services.com/blog/wp-content/uploads/2022/09/DDI_web-min-scaled.jpg)
![Thumbnail [90x90]](https://www.dbi-services.com/blog/wp-content/uploads/2025/05/JDE_Web-1-scaled.jpg)