If you want to play with Rancher you have several options, as outlined in the documentation. There are quick starts for the major public cloud providers (using Terraform), you can install it on a Linux host by using the Rancher container or you can do it on your own. We’ll be doing it step by step, as I believe that gives most information on how things actually work. We’ll start with one node and then extend the Kubernetes cluster to three nodes and you’ll notice that this is actually quite easy and convenient using Rancher.
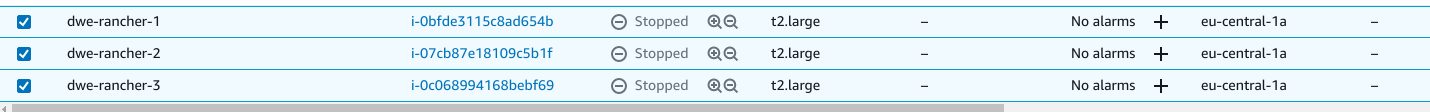
I’ve created three Debian 10 EC2 instances:
We’ll start with the first one, and once it is ready, bring it to the latest release:
admin@ip-10-0-1-168:~$ sudo apt update && sudo apt dist-upgrade -y && sudo systemctl reboot
Once it is back, lets give it a more meaningful hostname:
admin@ip-10-0-1-168:~$ sudo hostnamectl set-hostname rancher1 admin@ip-10-0-1-168:~$ sudo bash sudo: unable to resolve host rancher1: Name or service not known root@rancher1:/home/admin$ echo "10.0.1.168 rancher1 rancher1.it.dbi-services.com" >> /etc/hosts root@rancher1:/home/admin$ exit exit
As Rancher depends on Docker, we need to install a supported version of Docker. Range provides a script for this, which does all the work:
admin@ip-10-0-1-168:~$ sudo curl https://releases.rancher.com/install-docker/19.03.sh | sh
% Total % Received % Xferd Average Speed Time Time Time Current
Dload Upload Total Spent Left Speed
100 17251 100 17251 0 0 561k 0 --:--:-- --:--:-- --:--:-- 561k
+ sudo -E sh -c apt-get update
Hit:1 http://security.debian.org/debian-security buster/updates InRelease
Hit:2 http://cdn-aws.deb.debian.org/debian buster InRelease
Hit:3 http://cdn-aws.deb.debian.org/debian buster-updates InRelease
Hit:4 http://cdn-aws.deb.debian.org/debian buster-backports InRelease
Reading package lists... Done
...
+ sudo -E sh -c docker version
Client: Docker Engine - Community
Version: 19.03.15
API version: 1.40
Go version: go1.13.15
Git commit: 99e3ed8919
Built: Sat Jan 30 03:17:05 2021
OS/Arch: linux/amd64
Experimental: false
Server: Docker Engine - Community
Engine:
Version: 19.03.15
API version: 1.40 (minimum version 1.12)
Go version: go1.13.15
Git commit: 99e3ed8919
Built: Sat Jan 30 03:15:34 2021
OS/Arch: linux/amd64
Experimental: false
containerd:
Version: 1.4.3
GitCommit: 269548fa27e0089a8b8278fc4fc781d7f65a939b
runc:
Version: 1.0.0-rc92
GitCommit: ff819c7e9184c13b7c2607fe6c30ae19403a7aff
docker-init:
Version: 0.18.0
GitCommit: fec3683
If you would like to use Docker as a non-root user, you should now consider
adding your user to the "docker" group with something like:
sudo usermod -aG docker admin
Remember that you will have to log out and back in for this to take effect!
WARNING: Adding a user to the "docker" group will grant the ability to run
containers which can be used to obtain root privileges on the
docker host.
Refer to https://docs.docker.com/engine/security/security/#docker-daemon-attack-surface
for more information.
We’ll be using the Rancher Kubernetes Engine (RKE) and to get that onto the system, Rancher provides a single binary. Before proceeding with that, we need a user, configure sudo (for convenience), and create the ssh keys:
admin@ip-10-0-1-168:~$ sudo groupadd rancher admin@ip-10-0-1-168:~$ sudo useradd -g rancher -G docker -m -s /bin/bash rancher admin@ip-10-0-1-168:~$ sudo passwd rancher New password: Retype new password: passwd: password updated successfully admin@ip-10-0-1-168:~$ sudo bash root@rancher1:/home/admin$ echo "rancher ALL=(ALL) NOPASSWD: ALL" >> /etc/sudoers root@rancher1:/home/admin$ su - rancher rancher@rancher1:~$ ssh-keygen Generating public/private rsa key pair. Enter file in which to save the key (/home/rancher/.ssh/id_rsa): Created directory '/home/rancher/.ssh'. Enter passphrase (empty for no passphrase): Enter same passphrase again: Your identification has been saved in /home/rancher/.ssh/id_rsa. Your public key has been saved in /home/rancher/.ssh/id_rsa.pub. The key fingerprint is: SHA256:gHzFXkMttTw8dks64+1zEpt3Oef6TWs/pKoiYDDruIk rancher@rancher1 The key's randomart image is: +---[RSA 2048]----+ | ....o. | | . . .. +o.. | | o o. . oB o | | o . .. . * . | | + S + . | | . o . +.. | |o . . . ++o| |oo . . o=*B| |E. . ..... +X@| +----[SHA256]-----+ rancher@rancher1:~$ cat .ssh/id_rsa.pub >> .ssh/authorized_keys rancher@rancher1:~$ ssh rancher@rancher1 Linux rancher1 4.19.0-14-cloud-amd64 #1 SMP Debian 4.19.171-2 (2021-01-30) x86_64 The programs included with the Debian GNU/Linux system are free software; the exact distribution terms for each program are described in the individual files in /usr/share/doc/*/copyright. Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent permitted by applicable law.
That’s it for the requirements to get started. Download the RKE binary:
rancher@rancher1:~$ wget https://github.com/rancher/rke/releases/download/v1.1.15/rke_linux-amd64 rancher@rancher1:~$ mv rke_linux-amd64 rke rancher@rancher1:~$ sudo mv rke /usr/local/bin/ rancher@rancher1:~$ sudo chown rancher:rancher /usr/local/bin/rke rancher@rancher1:~$ sudo chmod 750 /usr/local/bin/rke rancher@rancher1:~$ rke --version rke version v1.1.15
All you need to do, to get RKE setup on a single host is this:
rancher@rancher1:~$ rke config [+] Cluster Level SSH Private Key Path [~/.ssh/id_rsa]: [+] Number of Hosts [1]: [+] SSH Address of host (1) [none]: 10.0.1.168 [+] SSH Port of host (1) [22]: [+] SSH Private Key Path of host (10.0.1.168) [none]: [-] You have entered empty SSH key path, trying fetch from SSH key parameter [+] SSH Private Key of host (10.0.1.168) [none]: [-] You have entered empty SSH key, defaulting to cluster level SSH key: ~/.ssh/id_rsa [+] SSH User of host (10.0.1.168) [ubuntu]: rancher [+] Is host (10.0.1.168) a Control Plane host (y/n)? [y]: [+] Is host (10.0.1.168) a Worker host (y/n)? [n]: y [+] Is host (10.0.1.168) an etcd host (y/n)? [n]: y [+] Override Hostname of host (10.0.1.168) [none]: [+] Internal IP of host (10.0.1.168) [none]: 10.0.1.168 [+] Docker socket path on host (10.0.1.168) [/var/run/docker.sock]: [+] Network Plugin Type (flannel, calico, weave, canal) [canal]: [+] Authentication Strategy [x509]: [+] Authorization Mode (rbac, none) [rbac]: [+] Kubernetes Docker image [rancher/hyperkube:v1.18.16-rancher1]: [+] Cluster domain [cluster.local]: [+] Service Cluster IP Range [10.43.0.0/16]: [+] Enable PodSecurityPolicy [n]: [+] Cluster Network CIDR [10.42.0.0/16]: [+] Cluster DNS Service IP [10.43.0.10]: [+] Add addon manifest URLs or YAML files [no]:
This creates the cluster configuration file:
rancher@rancher1:~$ ls -la cluster.yml -rw-r----- 1 rancher rancher 4619 Mar 6 14:40 cluster.yml
Bring it up:
rancher@rancher1:~$ rke up INFO[0000] Running RKE version: v1.1.15 INFO[0000] Initiating Kubernetes cluster INFO[0000] [dialer] Setup tunnel for host [10.0.1.168] ... INFO[0157] [addons] Successfully saved ConfigMap for addon rke-ingress-controller to Kubernetes INFO[0157] [addons] Executing deploy job rke-ingress-controller INFO[0162] [ingress] ingress controller nginx deployed successfully INFO[0162] [addons] Setting up user addons INFO[0162] [addons] no user addons defined INFO[0162] Finished building Kubernetes cluster successfully
That’s it. The one node Kubernetes cluster is ready (Control Plane, worker and etcd all on one host). This is of course nothing you’d do in a serious deployment, but to get started this is fine. To talk to the Kubernetes cluster you shoud install kubectl:
rancher@rancher1:~$ curl -LO "https://storage.googleapis.com/kubernetes-release/release/$(curl -s https://storage.googleapis.com/kubernetes-release/release/stable.txt)/bin/linux/amd64/kubectl"
% Total % Received % Xferd Average Speed Time Time Time Current
Dload Upload Total Spent Left Speed
100 38.3M 100 38.3M 0 0 73.9M 0 --:--:-- --:--:-- --:--:-- 73.8M
Same procedure as with the rke binary:
rancher@rancher1:~$ ls cluster.rkestate cluster.yml kube_config_cluster.yml kubectl rancher@rancher1:~$ sudo mv kubectl /usr/local/bin/ rancher@rancher1:~$ sudo chown rancher:rancher /usr/local/bin/kubectl rancher@rancher1:~$ sudo chmod 750 /usr/local/bin/kubectl
Use it to talk to your cluster:
rancher@rancher1:~$ export KUBECONFIG=kube_config_cluster.yml rancher@rancher1:~$ kubectl get namespace NAME STATUS AGE default Active 6m31s ingress-nginx Active 5m36s kube-node-lease Active 6m33s kube-public Active 6m33s kube-system Active 6m33s
Done. RKE is up and running on a single node. Be aware that we did not yet install Ranger, just RKE. But also notice how easy that was: We have a Kubernetes cluster running, and all we needed to do, took around 10 minutes. In the next post we’ll extend the configuration to three nodes.
![Thumbnail [60x60]](https://www.dbi-services.com/blog/wp-content/uploads/2022/08/DWE_web-min-scaled.jpg)
![Thumbnail [90x90]](https://www.dbi-services.com/blog/wp-content/uploads/2022/08/ADE_WEB-min-scaled.jpg)
![Thumbnail [90x90]](https://www.dbi-services.com/blog/wp-content/uploads/2022/08/NME_web-min-scaled.jpg)
![Thumbnail [90x90]](https://www.dbi-services.com/blog/wp-content/uploads/2022/08/GRE_web-min-scaled.jpg)