
Traditionally, the 3rd day is almost always the busiest and the most crowded in the sessions. I followed 4 breakout sessions, one 2 hours workshop and found some time to visit the Expo to see some sponsors and look for goodies 🙂
Confidential compute
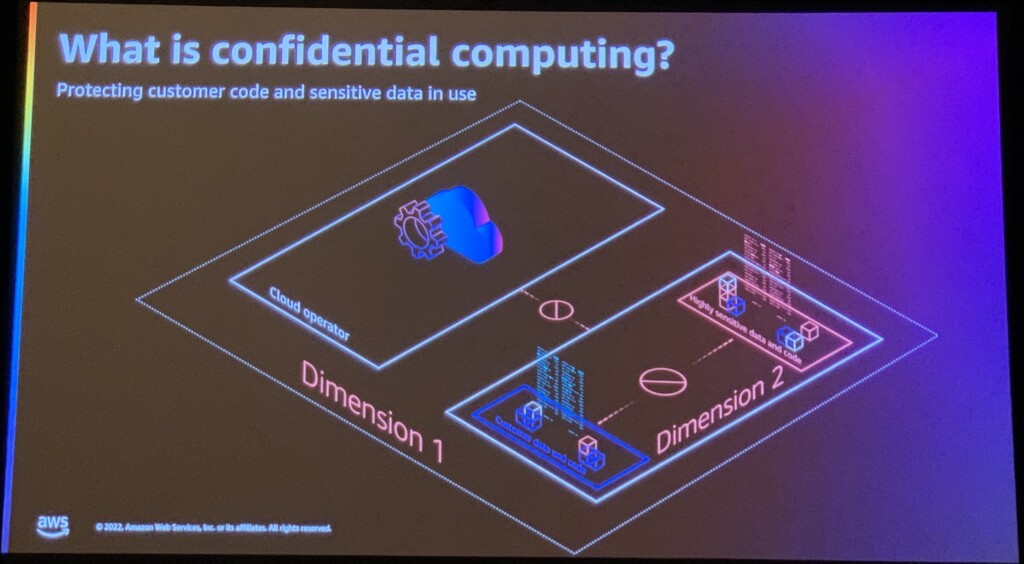
I have not really paid attention beforehand but I attended sessions mainly on security topics. I started with a presentation about confidential computing. Whether you are processing financial data, healthcare data or sensitive personal data, you most likely want to protect it. When speaking about protecting your data, you consider 2 dimensions:
- Dimension 1: protect from your the cloud operator (AWS in our example)
- Dimension 2: protect from your system administrators (i.e. segregation of duties).
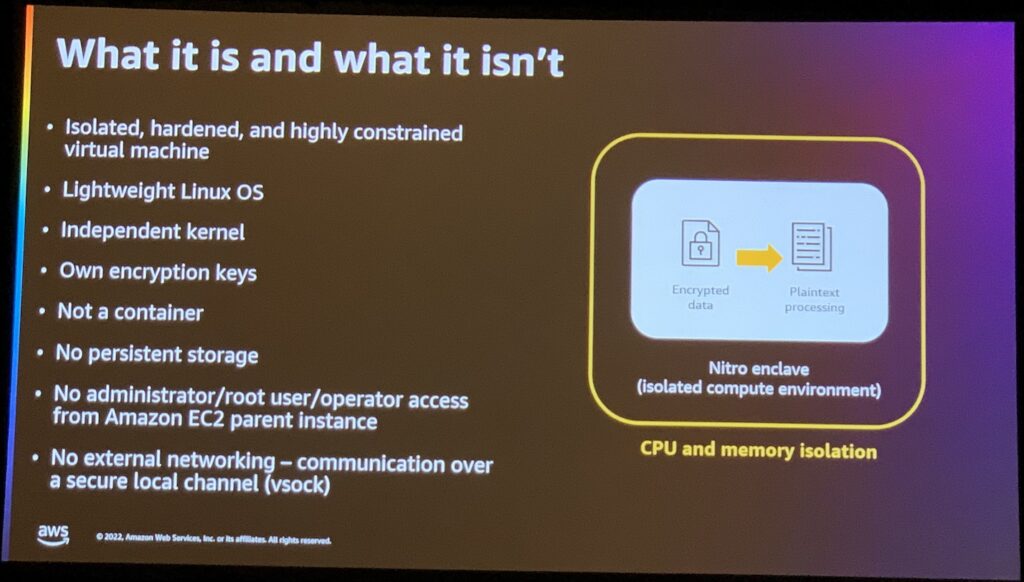
Firstly, the dimension 1 is covered by the AWS Nitro architecture itself. The system is designed in a way it does not allow any operator to access the system interactively. There are only administrative and audited APIs and none of them allow to access memory of running instances. As a consequence, it’s not possible for AWS support or operation team to perform live debug. But this trade-off has been decided right at the beginning to provide a more secure and trustful platform.
Secondly, AWS provides the feature “AWS Nitro Enclaves” to cover the dimension 2. In a first step, you encrypt your data. Then you decrypt the data and process it only from within the enclaves before sending it back to the storage encrypted. AWS Nitro Enclave proves its identity with a signature from the hypervisor itself. You get a guaranty on which code is running. Additionally, you also ensure the operators won’t access the data because there is no SSH or interactive access possible to the enclave.
S3 security best practices
Travel time between some hotels are really long here. Thanks to the content hub, I was able to follow 2 presentations without having to travel to another location. I attended a session about infrastructure as code but it may be the topic for another blog post.
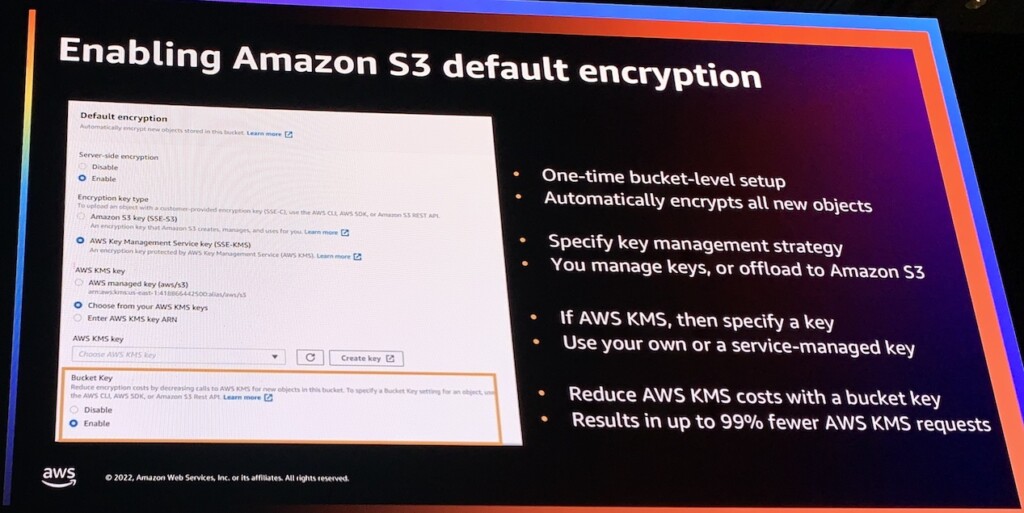
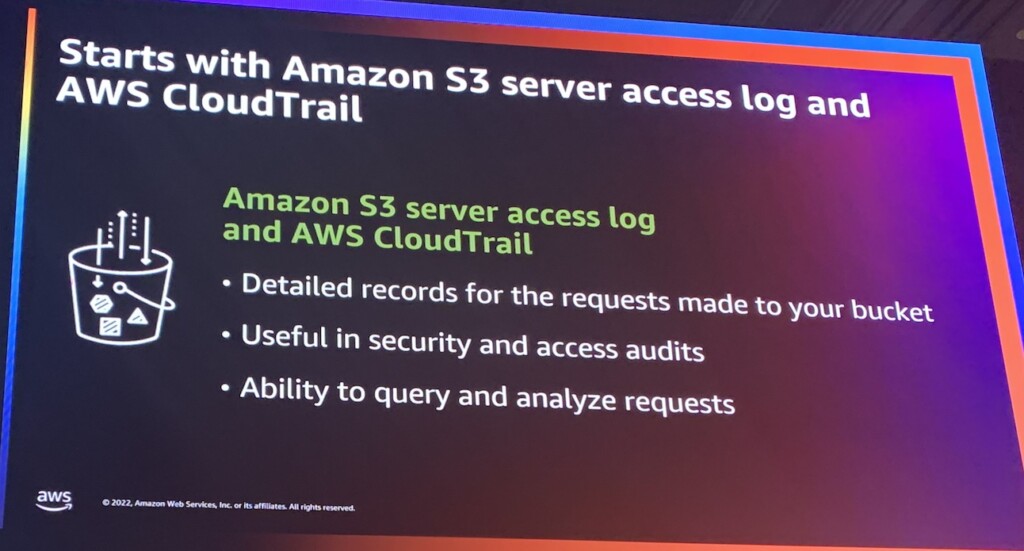
Let’s continue on security topics. I followed a session about S3 security best practices. I won’t go into all the details to keep this post readable. So here are 5 main points to secure your buckets:
- Enable “Block all public access”
- Encrypt your data
- Implement policy to control the encryption
- Enable Storage Lens to get insight about your data (including about encryption)
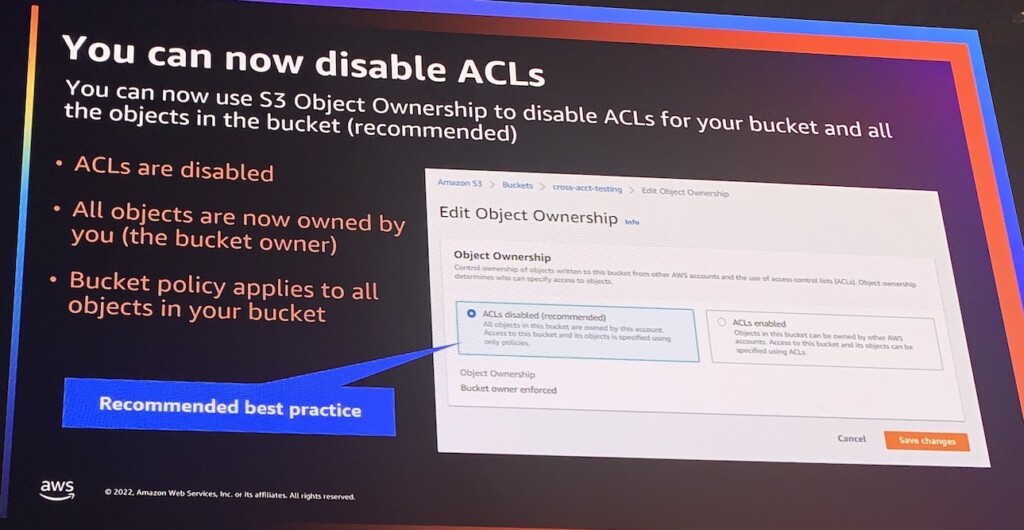
- Disable ACLs and use bucket policies for cross-account sharing
Network security in practice
After some much theoretical content about security, I really wanted to have some practice. Therefor I followed another workshop to get some experience. This workshop was in between the game jam and a classical workshop. Indeed by default, the full path was hidden and only some hints were provided.
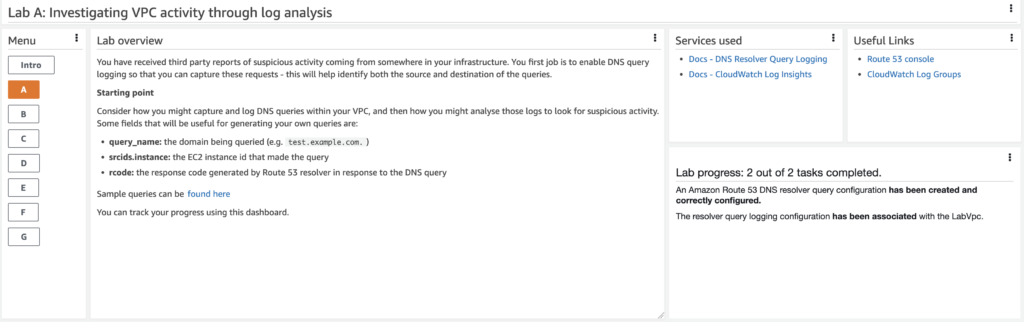
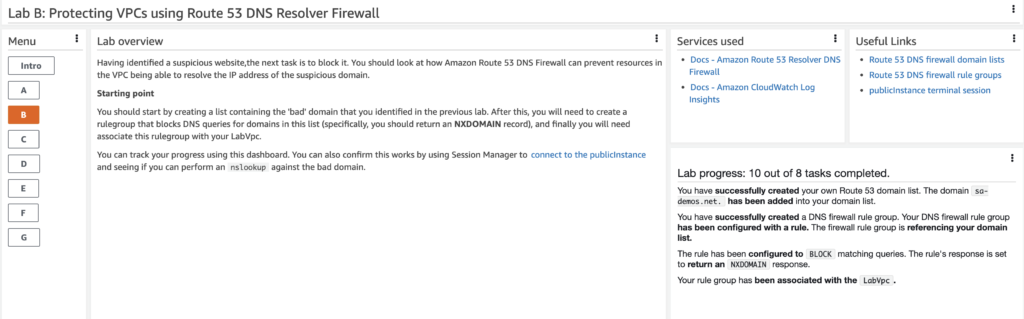
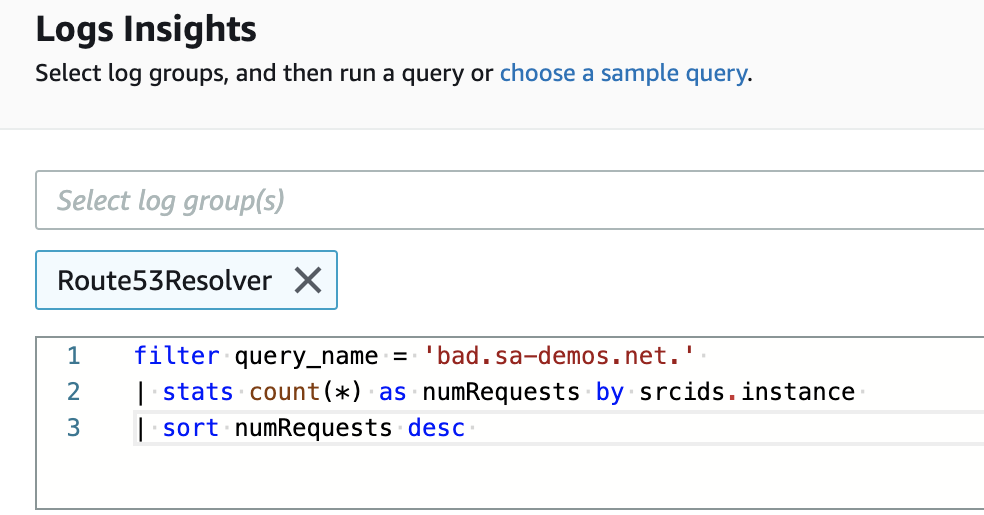
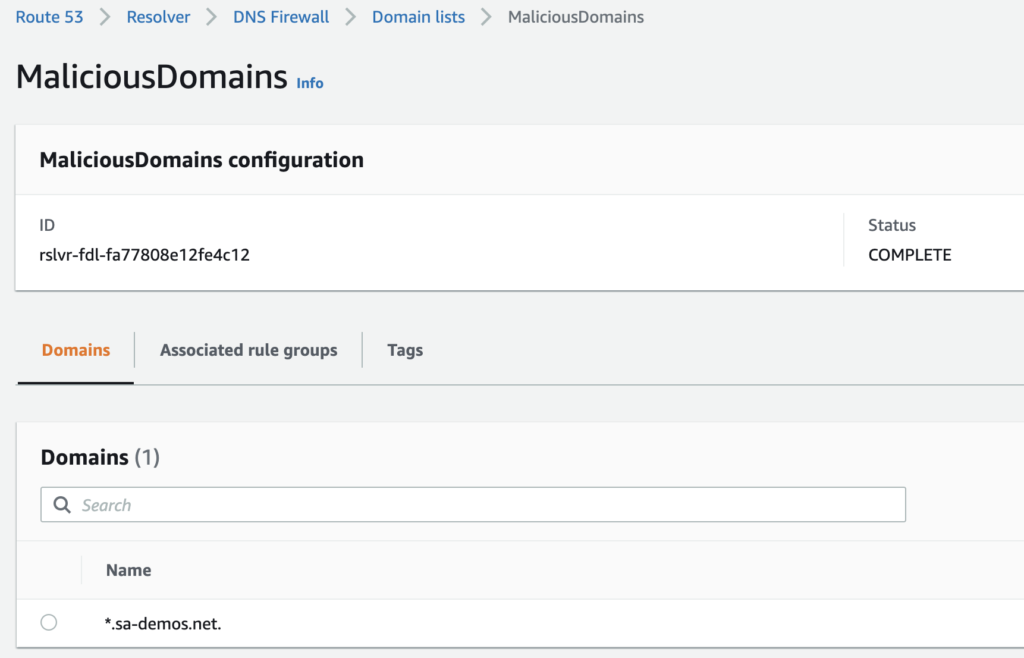
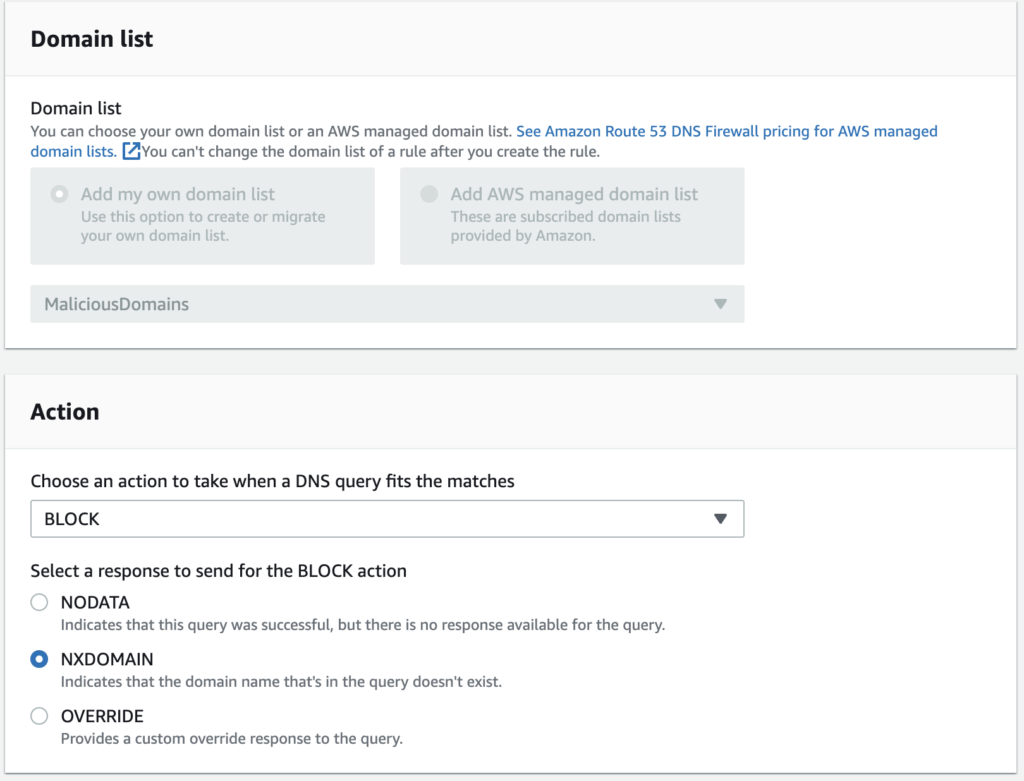
For the first exercice, our goal was to improve security on our DNS. We started by enabling monitoring to find suspicious activity. Then we queried the Route53 resolver logs using CloudWatch. You can write quite powerful queries in CloudWatch to explore your logs and for example find the instance calling a malicious domain. Finally Then we implemented DNS firewall and filtered the faulty domain in Route53.
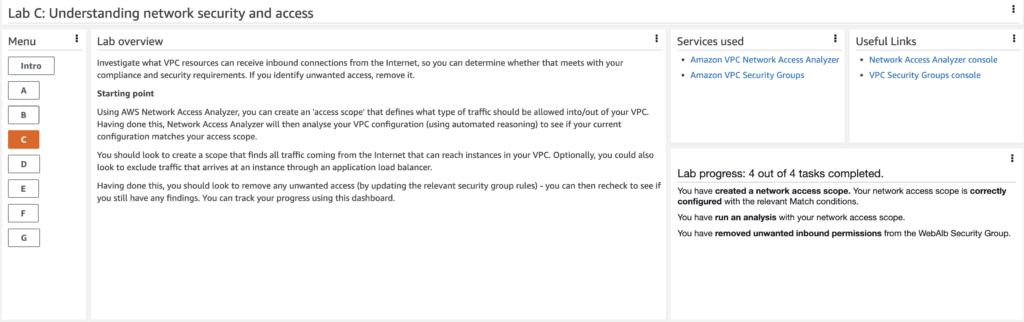
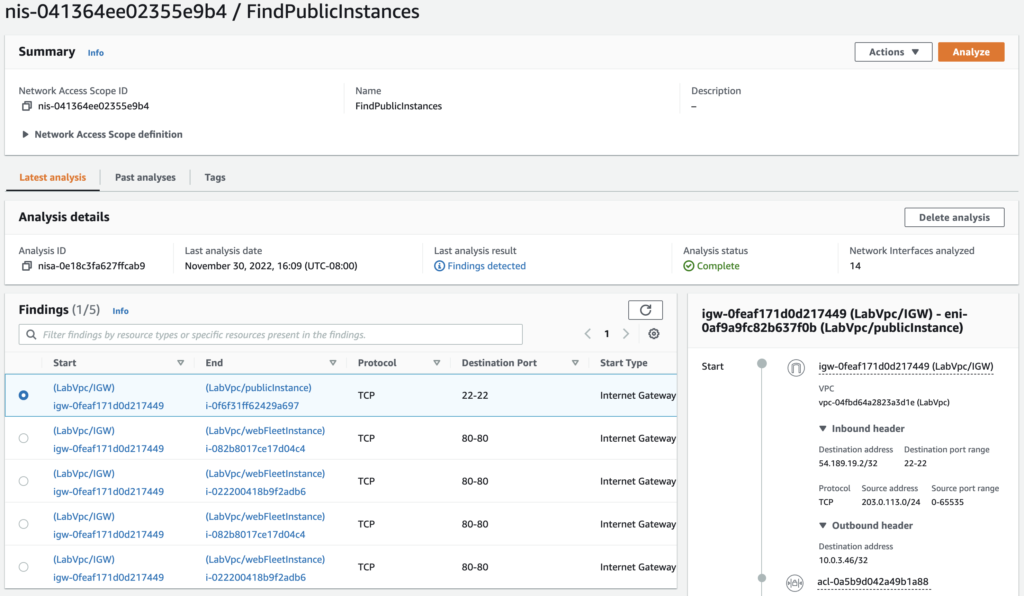
In another exercice, I used the Network Access Analyzer to find instances in my VPC reachable over internet. As for on-premise, I don’t recommend having instances being reachable directly over Internet unless fully under control. Once the analysis in complete, we spotted a misconfiguration and it allowed us to tighten the rules in the corresponding security group.
This workshop contained 7 different tracks, I cannot cover all in that blog. I really enjoyed it and it would be very nice to be able to replay it but it does not seem to be available outside of AWS events.
![Thumbnail [60x60]](https://www.dbi-services.com/blog/wp-content/uploads/2022/11/NIJ-min-scaled.jpg)
![Thumbnail [90x90]](https://www.dbi-services.com/blog/wp-content/uploads/2024/03/AHI_web.jpg)
![Thumbnail [90x90]](https://www.dbi-services.com/blog/wp-content/uploads/2025/07/ALK_MIN.jpeg)
![Thumbnail [90x90]](https://www.dbi-services.com/blog/wp-content/uploads/2025/05/JDE_Web-1-scaled.jpg)
![Thumbnail [90x90]](https://www.dbi-services.com/blog/wp-content/uploads/2022/08/ADE_WEB-min-scaled.jpg)